Ubuntu¶
Märkus
NitroPad T480s’i audio (pesa) port ei tööta automaatselt. Ühendatud kõrvaklappide käsitsi valimiseks installige programm pavucontrol ja valige ühendatud kõrvaklapid väljundseadmete all.
Plommitud riistvara kontrollimine¶
If you have ordered the unit with the option “sealed screws and sealed bag”, please verify the sealing before unpacking. If you do not know what this means, skip this section.
Turvaline stardiprotseduur¶
Enne esimest käivitamist peaksite tutvuma turvalise käivitamise protseduuriga.
Ümberehitus Ubuntu 24.04.¶
On olemas (probleem)mis takistab Ubuntul näidata luks dekrüpteerimise ekraani, kui see käivitatakse peaga. Tema on seal ja sa võid sisestada oma parooli pimesi, pärast seda Ubuntu käivitub normaalselt. Järgige neid samme:
Pead alustavad. Kui midagi ei ole vaja teha, käivitub Ubuntu automaatselt
Mõne aja pärast näete musta ekraani, mille viimased read on valged:
Locking TPM2 platform hierarchy... Starting the new kernel
Need read näitavad, et Ubuntu käivitub.
Oodake 5 sekundit ja seejärel sisestage oma salasõna („12345678“, kui käivitate selle esimest korda), millele järgneb Sisestage.
Nüüd näete tavalist Ubuntu ekraani. Esmakordsel käivitamisel peate lõpetama algkonfiguratsiooni.
Alustamine¶
Pärast ostu sooritamist on paroolid määratud vaikimisi ja neid peate ise muutma:
Vajutage Enter („Default Boot“) pärast süsteemi käivitamist, kui NitroPad ei ole näidanud ühtegi viga ja Nitrokey põleb roheliselt (vt eespool).
Seejärel palub süsteem sisestada kõvaketta dekrüpteerimiseks salasõna. Salasõna on esialgu „12345678“. Seda muudeti 10.04.2024, nii et kui „12345678“ ei tööta, proovige vana vaikimisi: „PleaseChangeMe“.
Seejärel juhatab süsteem teid läbi kasutajakonto loomise protsessi. Pärast seda peaksite süsteemi edukalt käivitama ja seda juba normaalselt kasutama.
Open the pre-installed Nitrokey App and change the PINs of your Nitrokey. To learn more about how to change the PINs, please refer to chapter Change User and Admin PIN.
Muutke kettakrüpteerimise salasõna. Lisateavet selle kohta, kuidas muuta ketta krüpteerimise salasõna, leiate peatükist Ketta krüpteerimise salasõna muutmine. See parool erineb teie kasutajakonto paroolist’see parool on erinev.
Käitumine pärast süsteemi uuendamist¶
The NitroPad and NitroPC firmware checks certain system files for changes. If your operating system has updated important components, you will be warned the next time you boot the NitroPad or NitroPC. This could look like this, for example:
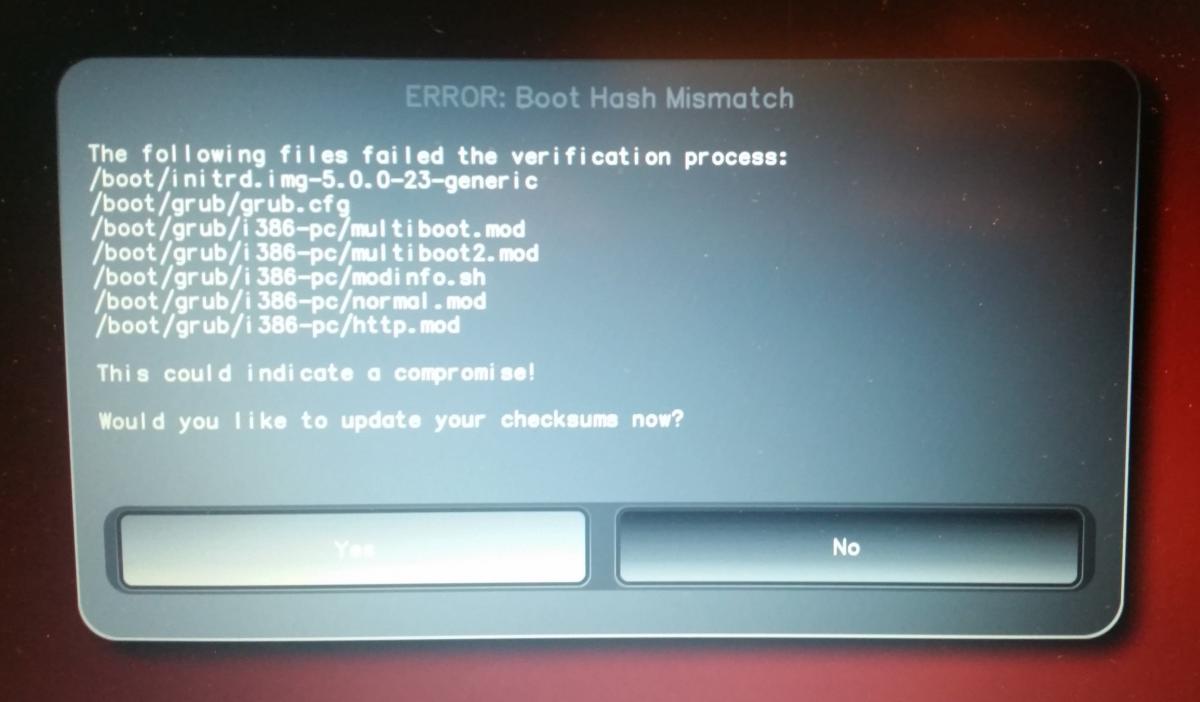
That’s why it’s important to restart your NitroPad or your NitroPC under controlled conditions after a system update. Only when the new status has been confirmed can you leave the device unattended again. Otherwise, you will not be able to distinguish a possible attack from a system update. Detailed instructions for a system update can be found here.