Ubuntu¶
Opomba
Zvočni priključek (jack) na napravi NitroPad T480s ne deluje samodejno. Če želite ročno izbrati priključene slušalke, namestite program pavucontrol in izberite priključene slušalke v razdelku Output Devices.
Preverjanje zapečatene strojne opreme¶
If you have ordered the unit with the option “sealed screws and sealed bag”, please verify the sealing before unpacking. If you do not know what this means, skip this section.
Postopek varnega zagona¶
Pred prvim zagonom se morate seznaniti s Postopek varnega zagona.
Workaround Ubuntu 26.04 & 24.04.¶
There is an issue that prevents Ubuntu to show the LUKS decryption screen, if started with heads. It’s there and you can type in your password blindly, after that Ubuntu starts normal. Follow these steps:
Heads starts. If nothing needs to be done, Ubuntu will start automatically.
Čez nekaj časa se bo prikazal črn zaslon z belim napisom v zadnjih vrsticah:
Locking TPM2 platform hierarchy... Starting the new kernel
Te vrstice kažejo, da se Ubuntu začenja.
Počakajte 5 sekund in nato vnesite geslo **** („12345678“, če ga zaganjate prvič), nato pa Vnesite.
Zdaj se bo prikazal običajen zaslon Ubuntuja. Ob prvem zagonu morate dokončati začetno konfiguracijo.
Začetek¶
Po nakupu so gesla nastavljena na privzeto vrednost in jih morate spremeniti sami:
Po zagonu sistema pritisnite Enter („Default Boot“), če naprava NitroPad ni pokazala nobenih napak in če je tipka Nitrokey zeleno osvetljena (glejte zgoraj).
Nato vas bo sistem pozval k vnosu gesla za dešifriranje trdega diska. Na začetku je geslo „12345678“. To je bilo spremenjeno v različici 10.04.2024, zato, če „12345678“ ne deluje, poskusite s starim privzetim geslom: „PleaseChangeMe“.
Sistem vas bo nato vodil skozi postopek ustvarjanja uporabniškega računa. Po tem morate uspešno zagnati sistem in ga že lahko normalno uporabljate.
Open the pre-installed Nitrokey App and change the PINs of your Nitrokey. To learn more about how to change the PINs, please refer to chapter Change User and Admin PIN.
Spremenite geslo za šifriranje diska. Če želite izvedeti več o tem, kako spremeniti geslo za šifriranje diska, glejte poglavje Premeni geslo za šifriranje diska. Ta geslofraza se razlikuje od gesla vašega uporabniškega računa.
Obnašanje po posodobitvi sistema¶
The NitroPad and NitroPC firmware checks certain system files for changes. If your operating system has updated important components, you will be warned the next time you boot the NitroPad or NitroPC. This could look like this, for example:
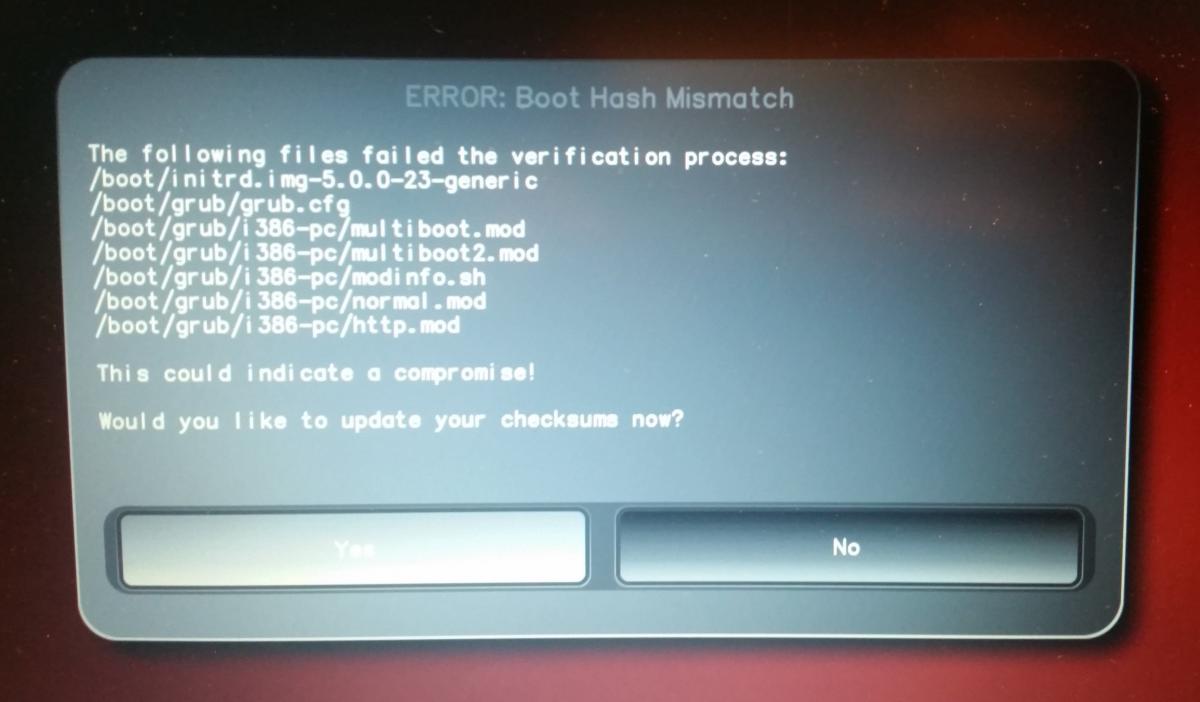
That’s why it’s important to restart your NitroPad or your NitroPC under controlled conditions after a system update. Only when the new status has been confirmed can you leave the device unattended again. Otherwise, you will not be able to distinguish a possible attack from a system update. Detailed instructions for a system update can be found here.