QubesOS¶
Bemærk
Lydporten (jackstik) på NitroPad T480s fungerer ikke automatisk. Hvis du vil vælge en tilsluttet hovedtelefon manuelt, skal du installere programmet pavucontrol og vælge den tilsluttede hovedtelefon under Output Devices.
Verifikation af forseglet hardware¶
If you have ordered the unit with the option “sealed screws and sealed bag”, please verify the sealing before unpacking. If you do not know what this means, skip this section.
Procedure for sikker opstart¶
Før første start bør du gøre dig bekendt med Sikker startprocedure.
Kom godt i gang¶
Efter købet er adgangskoderne indstillet til en standardværdi og skal ændres af dig:
Tryk på Enter (»Default Boot«) efter opstart af systemet, forudsat at NitroPad ikke har vist nogen fejl, og at Nitrokey er grønt lysende (se ovenfor).
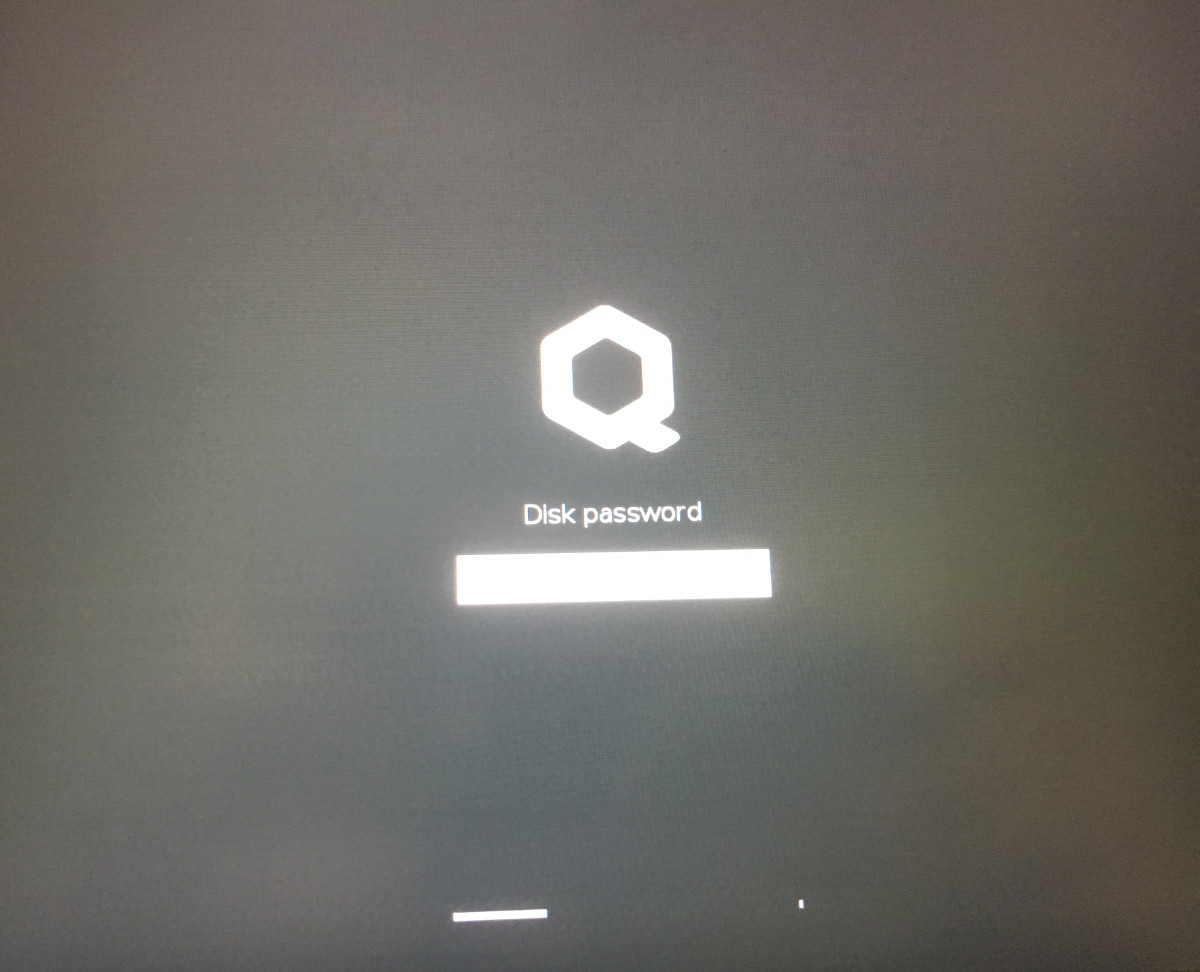
Next, the system will prompt you to enter the passphrase to decrypt the hard disk. The passphrase is initially »12345678«.
Systemet vil derefter guide dig gennem processen med at oprette en brugerkonto. Herefter skulle du have startet systemet op og allerede kunne bruge det normalt.
Open the pre-installed Nitrokey App and change the PINs of your Nitrokey as described here.
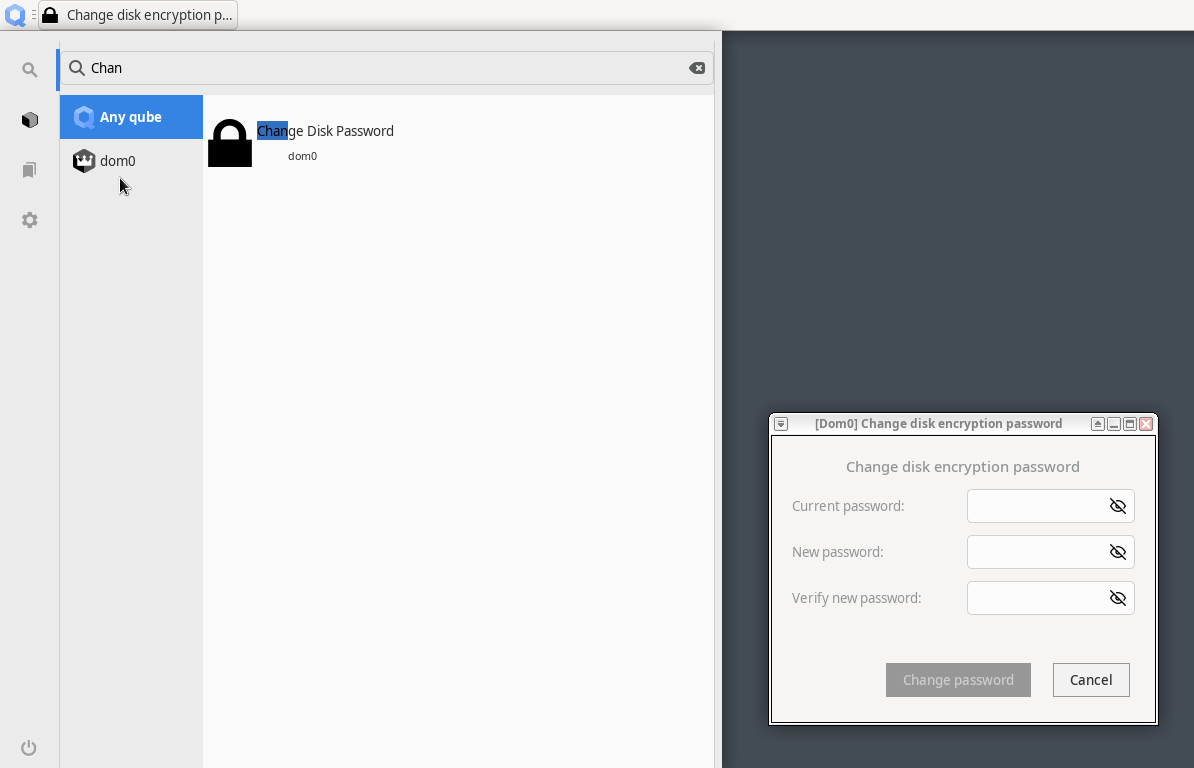
Skift passphrase til harddiskkrypteringen ved at søge i Qubes-menuen efter »Change Disk Passwort«. Denne passphrase er forskellig fra din brugerkontos passphrase.
NitroPads leveres med det seneste installationsbillede af Qubes OS, som skal opdateres efter installationen, fordi det ikke indeholder alle de seneste sikkerhedsrettelser. For at opdatere skal du bruge Update Manager som beskrevet i Qubes Documentation.
Bemærk
Specifikt for NitroPad V54 indeholder Qubes 4.2.3 installationsbillede en fejl, der begrænser til kun at bruge den højeste skærmopløsning. Dette er rettet, når du har opdateret dom0 og genstartet.
Adfærd efter en systemopdatering¶
The NitroPad and NitroPC firmware checks certain system files for changes. If your operating system has updated important components, you will be warned the next time you boot the NitroPad or NitroPC. This could look like this, for example:
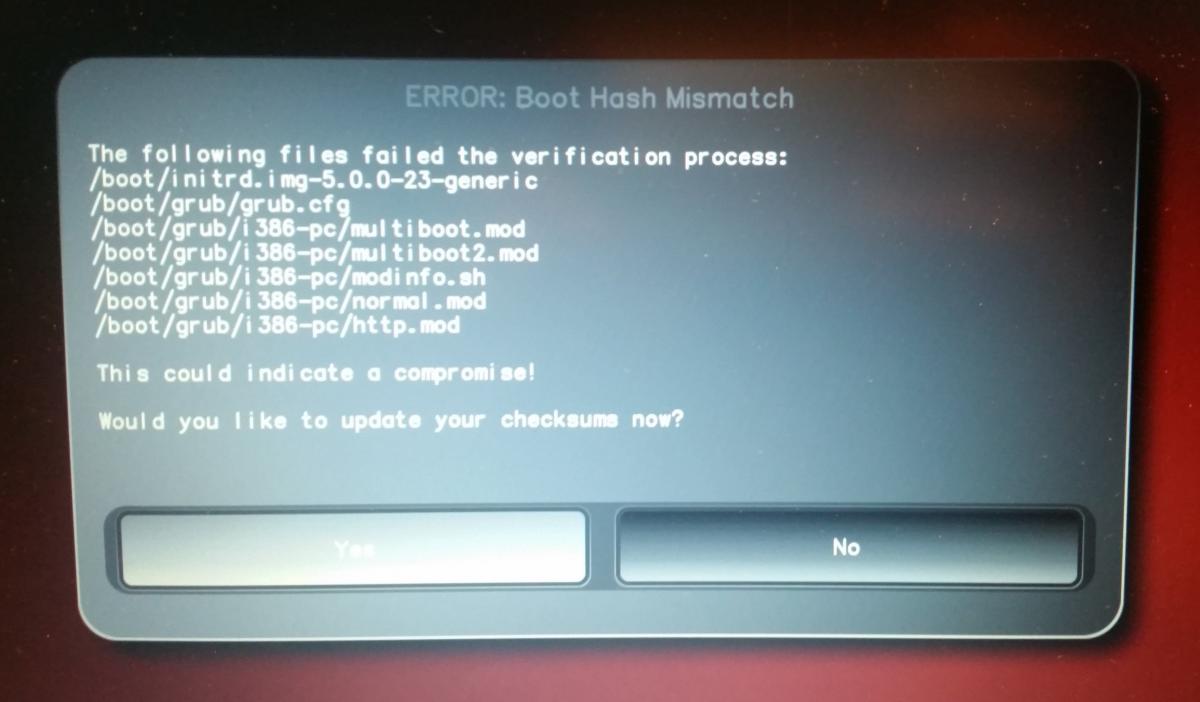
That’s why it’s important to restart your NitroPad or your NitroPC under controlled conditions after a system update. Only when the new status has been confirmed can you leave the device unattended again. Otherwise, you will not be able to distinguish a possible attack from a system update. Detailed instructions for a system update can be found here.
Failed to Start Load Kernel Modules¶
Under opstart af systemet vises fejlen »Failed to start Load Kernel Modules« (Fejl ved start af Load Kernel Modules«). Dette er et kendt problem, som ikke er kritisk og kan ignoreres.