Login to Windows Domain Computers With MS Active Directory¶
Compatible Nitrokeys |
|||||||
|---|---|---|---|---|---|---|---|
✓ active |
⨯ inactive |
✓ active |
✓ active |
⨯ inactive |
✓ active |
⨯ inactive |
⨯ inactive |
Download and install the latest OpenSC.
Use a text editor to add the following settings to
C:\Program Files:\OpenSC Project\OpenSC\opensc.conf.# Nitrokey Pro 2, OpenPGP Card, Nitrokey Storage 2 card_atr 3b:da:18:ff:81:b1:fe:75:1f:03:00:31:f5:73:c0:01:60:00:90:00:1c { type = 9002; driver = "openpgp"; # name = "Nitrokey Pro 2"; md_read_only = false; md_supports_X509_enrollment = true; } # Nitrokey Pro, OpenPGP Card card_atr 3B:DA:18:FF:81:B1:FE:75:1F:03:00:31:C5:73:C0:01:40:00:90:00:0C { type = 9002; driver = "openpgp"; # name = "Nitrokey Pro"; md_read_only = false; md_supports_X509_enrollment = true; } # Nitrokey HSM 2, SmartCard-HSM card_atr 3b:de:18:ff:81:91:fe:1f:c3:80:31:81:54:48:53:4d:31:73:80:21:40:81:07:1c { type = 26000; driver = "sc-hsm"; # name = "Nitrokey HSM 2"; md_read_only = false; md_supports_X509_enrollment = true; } # Nitrokey HSM, SmartCard-HSM card_atr 3B:FE:18:00:00:81:31:FE:45:80:31:81:54:48:53:4D:31:73:80:21:40:81:07:FA { type = 26000; driver = "sc-hsm"; # name = "Nitrokey HSM"; md_read_only = false; md_supports_X509_enrollment = true; }Open a command terminal and enter “regedit”. Use regedit to import this file.
Now you can enroll Nitrokeys for your users managed in Microsoft Active Directory. You may either use Microsoft PKI, gpgsm, or Smart Policy. The following steps describe the usage of Smart Policy.
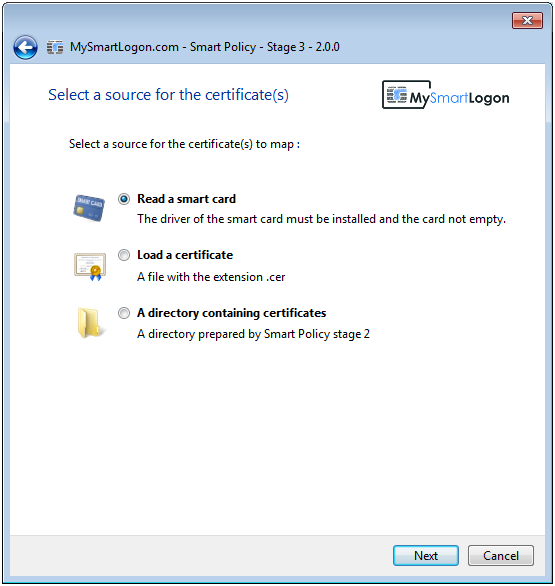
Download and install Smart Policy.
Select “Read a smart card”
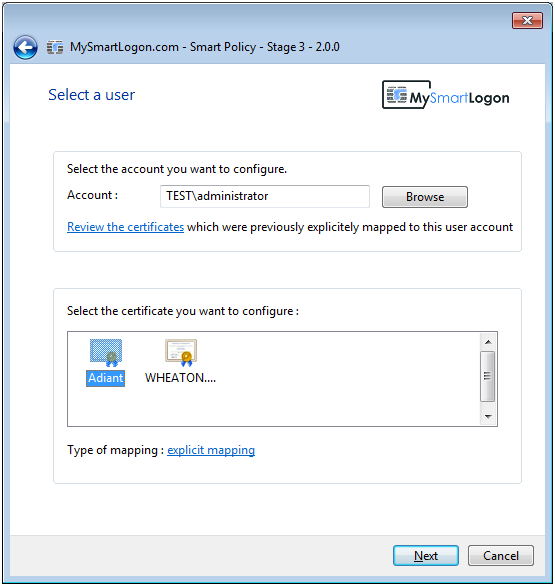
Select the certificate, mapping, and user.
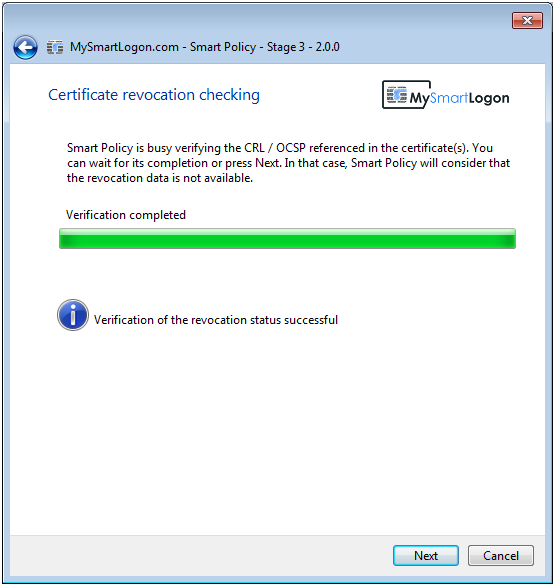
Verify the device status via CRL.
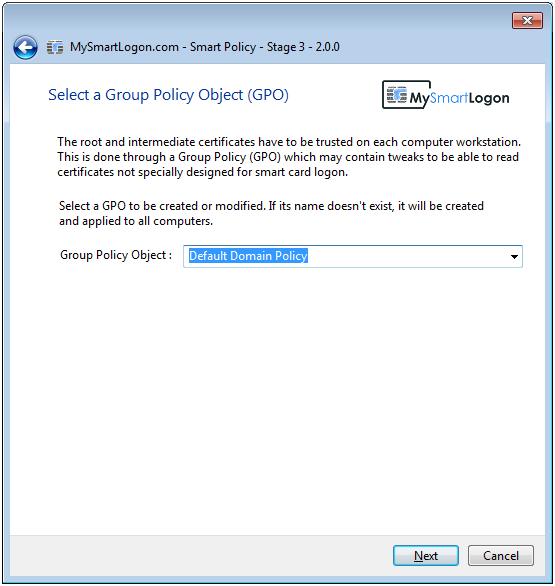
Choose a Group Policy Object (GPO).
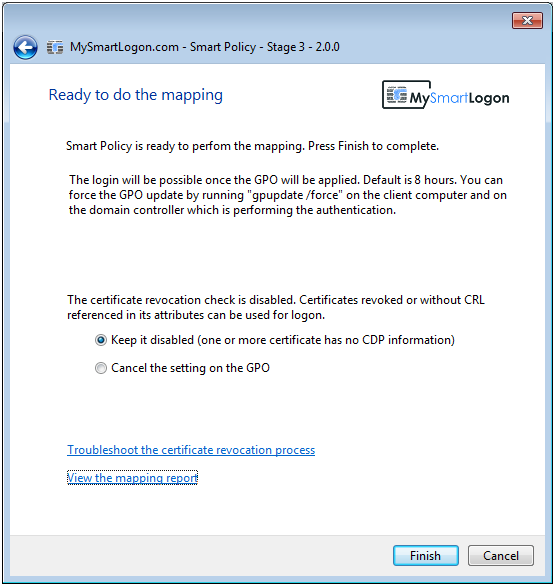
Confirm applying the mapping.
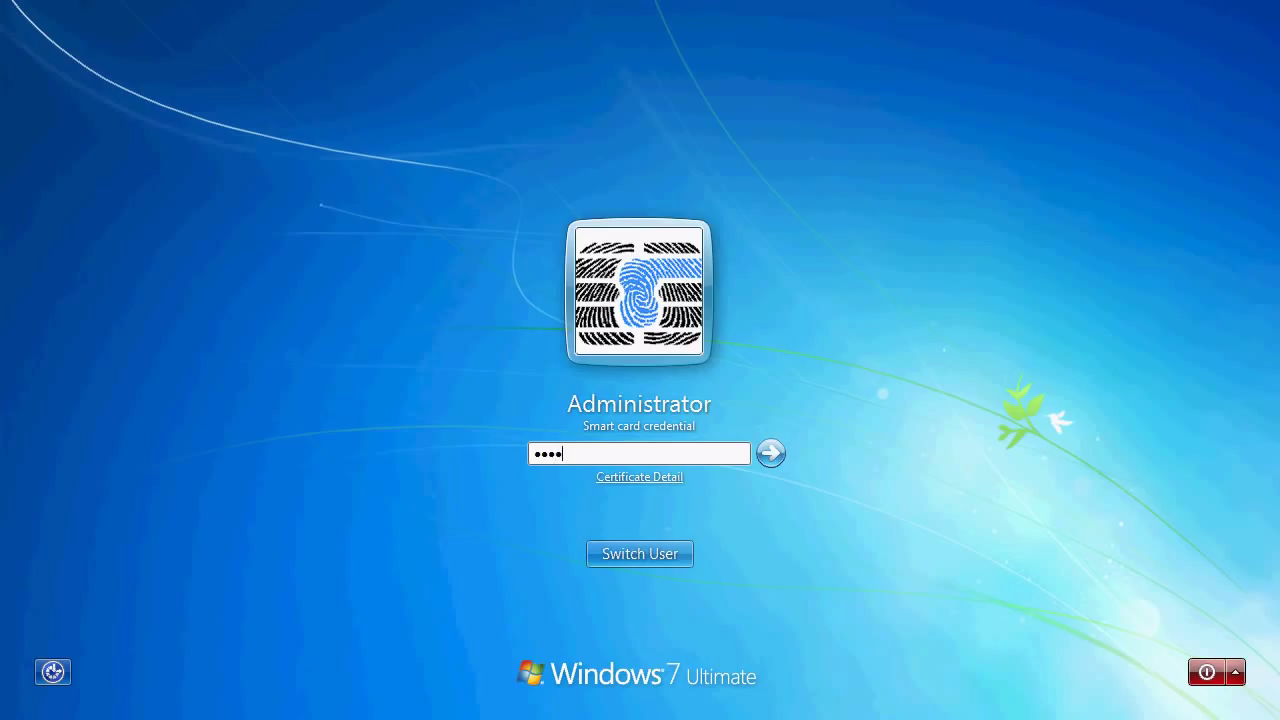
From now on, when logging on to your Windows computer you need to connect the Nitrokey and enter your PIN.